Introduction
As a Windows service, RPM Remote Print Manager® ("RPM") cannot access shared printers on your network or shared folders.
For that reason, we added support for login credentials for any printer or folder device in RPM. You can also access shared printers or folders from a filter action in this same way.
Your Windows network protects shared printers and folders using login credentials. Credentials prevent people from outside your network from getting access to your printers and folders unless they have a valid login.
Shared printers use login credentials
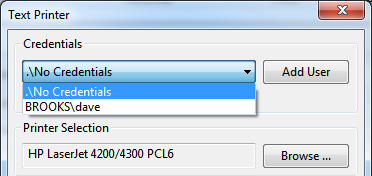
Let's look at the credentials used for a text print action. The other actions that use credentials work much the same way.
The credentials droplist is at the top. Notice that "no credentials" is the default. Also shown are credentials for the BROOKS domain and the user 'dave' because that was the logged-in user when we ran the user interface. If we selected "BROOKS\dave" then this action would use Dave's login credentials, and any printer or shared drive that Dave can access when he's logged in would also be available to RPM.
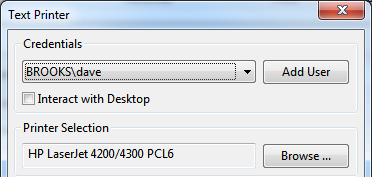
If we had previously selected "dave" the form would show that:
Now let's add a user. Click the Add User button.
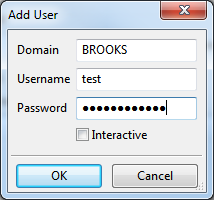
Here we have entered the user test in the BROOKS domain and entered a password. RPM will store the password encrypted; it never passes "over the wire" as clear text.
We explain the "Interactive" checkbox explained below.
Once we click OK, these login credentials are available to any action in RPM. Of course, you would have to select those credentials to use them.
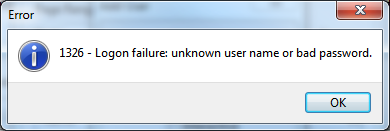
The only caveat to creating credentials is that the RPM user interface checks the user and password before storing. If you have a non-existent user or wrong password you'll see this:
What happens when we text print with credentials
Any time RPM runs an action on a print job, the resources for that action are separate from the rest of RPM's processing. If you have configured RPM to use login credentials for that action, then only that action will have those credentials.
It works more or less like this:
- RPM does a temporary login using the credentials
- RPM does the one action
- RPM logs off
The rights of that login will not "leak" into any other processing RPM is doing. The rights are isolated to the action performed on that print job, and only to that action and that print job.
Other actions with credentials
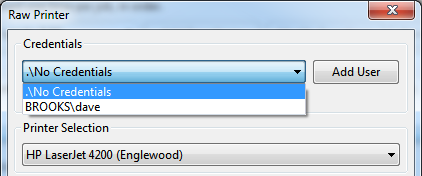
Just like the Text print action, the Raw print action uses credentials:
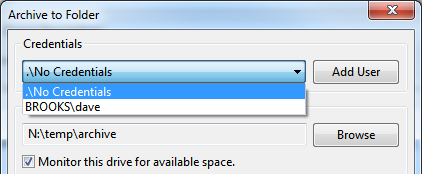
The Archive to Folder action uses credentials to write to shared file systems:
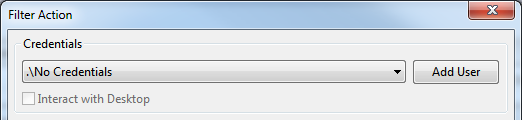
Similarly, the filter action uses credentials and has the 'interact with desktop' option:
Interactive processing
One thing we found with printing is that Windows expects that print drivers do not need the user's desktop, but in actual practice, this is often not the case. For example, we noticed for some printers, you could print just fine in a regular login session, but nothing happened when you tried to print from the RPM service.
We overcame this by giving actions the ability to interact with the desktop.
When you print with the Interactive setting, you should be able to see any printer dialogs or status you need to. We recommend that the credentials for the print action be the same as your standard Windows login.
When you run a filter with "interact with desktop, " you'll be able to see the program on your desktop. So, for instance, you can use the Windows Notepad application as a filter and view your print jobs in a window.
Critical event notification
It's typical (and highly recommended) for network users to change passwords occasionally. The only problem with this is RPM running in the background. The action will fail as soon as RPM attempts to execute an action with updated credentials.
Unfortunately, this has often been time-consuming to track down.
That kind of situation is the reason we added critical events. The user interface keeps a table of critical events available via the View menu. This way, you have a quick report of situations RPM has identified that could be a problem. The user interface also supports Windows notifications, so if you happen to be logged in when a critical event occurs, you can see them in the notification channel if you like.
